A few months ago it was brought to our attention that disabled users were still able to sign-in to Lync. Thinking this was crazy talk I set out to figure out how this was possible, and stumbled across Jeff Guillet’s article Disabling a User in AD Does Not Disable the User In Lync. Wanting to understand the process better I tested Jeff’s findings on Lync Server 2013.
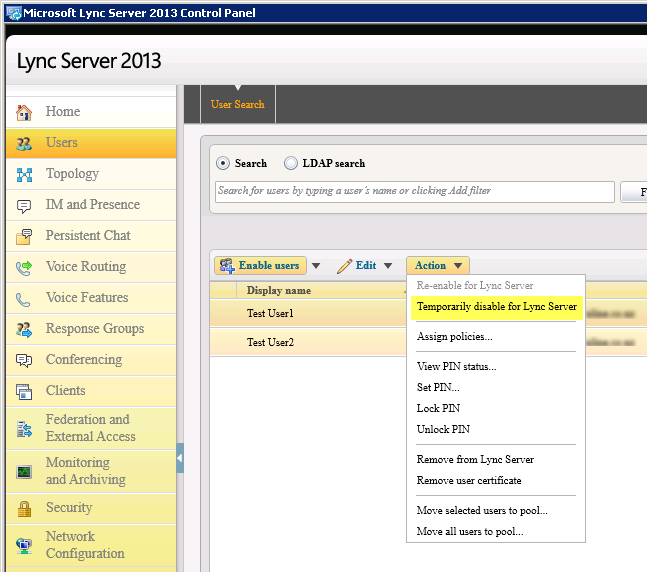
Lync Server has 3 options when it comes to authentication – Kerberos, NTLM, and certificate based. Kerberos is the default authentication method for authenticating clients on the domain, while NTLM is used when authenticating externally via the Lync Edge servers. If the user selects “Save my password” during sign-in, Lync server will generate a X.509 certificate and publish it to the RTC database, as well as the current users local certificate store on their PC. The certificate is valid for 180 days and will be used for authentication from then on, and as a result the users AD account will not be checked during sign-in. The certificate can be revoked or deleted from the client to enforce re-authentication using domain credentials, however this will not affect signed in users immediately, and its interesting to note that if the domain credentials are still valid, they will still sign automatically downloading a new certificate in the process. For near immediate results you should use the Lync Server Control Panel to “Temporarily disable for Lync Server”. Needless to say that this step should be added to your employee leaving procedures to ensure that access is completely disabled.
Check it out for yourself:
- Create an Active Directory test user
- Enable the account for Lync
- Login to the Lync client with the new test account, making sure not to select the “Save my password” option
- Check the Lync Front End security logs and you will see the login event for the user
- Under the current users personal certificate store you will see a certificate issued by Lync for the sign-in name:
- If you haven’t already, install the Lync Resource Kit on your Lync Front End server (see here)
- From the Lync Front End server open command prompt and browse to the Lync Resource Kit directory (For Lync 2013 – C:Program FilesMicrosoft Lync Server 2013ResKit)
- Run dbanalyze.exe /report:user /user:<test user UPN> /sqlserver:<FQDN of Lync Server>RTCLocal
- At the bottom of the report there will be information about the certificates that have been issued – Device ID, Publication Time, and Expiration Date. Regardless of whether the “Save my password” option is selected, a server certificate will exist for the user, and user could have more than 1 certificate if they have logged in to multiple PC’s:
- Run Get-CsClientCertificate <test user> from the Lync Management Shell and you will also see the certificate
- Now logoff Lync
- Check the Lync Front End security logs and you will see the logoff event for the user
- Under the current users personal certificate store you will see that the previously issued certificate has been removed
- Run the dbanalyze.exe command again from step 8 and you will see that the certificate still exists on the server
- Run Get-CsClientCertificate <test user> from the Lync Management Shell and you will see the certificate still exists on the server
- Now this time login to Lync, this time selecting the “Save my password” option. Lync 2013 will prompt you to confirm you want to save your sign-in information
- Logoff Lync
- Check the Lync Front End security logs and you will notice that login and logoff events are no longer recorded. I can only assume this is because we are now using certificate authentication
- Under the current users personal certificate store you will see that the previously issued certificate still exists. This will be used to authenticate the users future login attempts
- Now go and disable the AD account
- Try and sign-in to Lync and see what happens. Amazingly you’re still be able to sign in!!! This will continue to be the case until you delete the client sign-in information or associated client certificate, or run Revoke-CsClientCertificate from the Lync Management Shell.
- Lets delete the AD account and see what happens
- Now try and sign-in to Lync and see what happens. Whew we can no longer sign-in!
- Run the dbanalyze command in step 8 again. This time you should get the following error – “There was an error communicating with the database:###50010:ReportUserData:[email protected] is not found in this database”
- Run Get-CsClientCertificate <test user> from the Lync Management Shell. This time you will get the following error “Cannot find user in Active Directory”
PowerShell
PowerShell could come to the rescue to simplify the administrative effort when disabling users. You could run one of the following 2 options as a scheduled task, which would ensure that the additional steps are taken to stop disabled users logging in to Lync.Disable Lync for all users who have a disabled AD account – This is a good option if the users will no be re-enabled at a later date:
|
1 2 3 4 |
$x = Get-CsAdUser | Where-Object {$_.UserAccountControl -match "AccountDisabled" -and $_.Enabled} $x | Disable-CsUser write-host "`nThe following users have been disbaled for Lync:" $x.Name |
Revoke the client certificate for users who have a disabled AD account – This option will revoke the client certificate and ensure the user has to re-authenticate using domain credentials before being able to download a new one:
|
1 2 3 4 |
$x = Get-CsAdUser | Where-Object {$_.UserAccountControl -match "AccountDisabled" -and $_.Enabled} $x | Revoke-CsClientCertificate write-host "`nThe following users Lync certificates have been revoked:" $x.Name |




















Thanks Andrew for the detailed explanation… 🙂
Cheers for the feedback, glad it helped 🙂
Your line to disable the users is overly coded. Take a look at http://www.ehloworld.com/265, where I show
Get-CsAdUser | ?{$_.UserAccountControl -match "AccountDisabled" -and $_.Enabled -eq $true} | Disable-CsUser
will work. And actually,
Get-CsAdUser | ?{$_.UserAccountControl -match "AccountDisabled" -and $_.Enabled} | Disable-CsUser
should work as well.
Cheers Pat, I'll give it a test run and update my post accordingly. One question – does selecting the object properties to return speed up the query, or is your example of piping it into a where statement just as quick?
Select-Object is more if you're going to display the results. It's not needed when piping to another cmdlet.
As for the second method, you generally don't have to test if something is $true. Merely that it exists. Again, as mentioned in my blog post, you may not want to disable ALL accounts that are AD disabled. An example are accounts that are configured for health monitoring configuration, which can be AD disabled for security purposes.
Cheers Pat, great blog post. I have updated as per your recommendation, and added an output showing the effected user accounts.
Hello! I’ve been reading your web site for a while now and finally
got the bravery to go ahead and give you a shout out from Porter Tx!
Just wanted to say keep up the excellent work!
Cheers, appreciated!
it’s really good post but if users disabled and not removed/disabled from Lync, is there any impact for Database or Lync/Skype infrastructure, like.. monitoring reports, counts etc.
Cheers! I’m not 100% sure off the top of my head, but I would assume not based on my understating – should be fine.
Best description i’ve read about this on the Internet. Explanatory and detailed.
How do i schedule this script to run once a day and also send report to a particular email?
Thanks as i anticipate your response.
Hey and thanks for the feedback! Use Task Scheduler in Windows to create a task that runs one of the scripts mentioned in this article. This article will help you – http://blogs.technet.com/b/heyscriptingguy/archive/2012/08/11/weekend-scripter-use-the-windows-task-scheduler-to-run-a-windows-powershell-script.aspx
[…] and If you disable a user in AD they can still use Lync (at least for some time). Have a look at https://ucgeek.co/2014/04/lync-users-can-login-after-domain-account-disabled/ for some deeper details. My concern wasn’t about the fact that the users still can use Lync […]